Ensuring Election Integrity
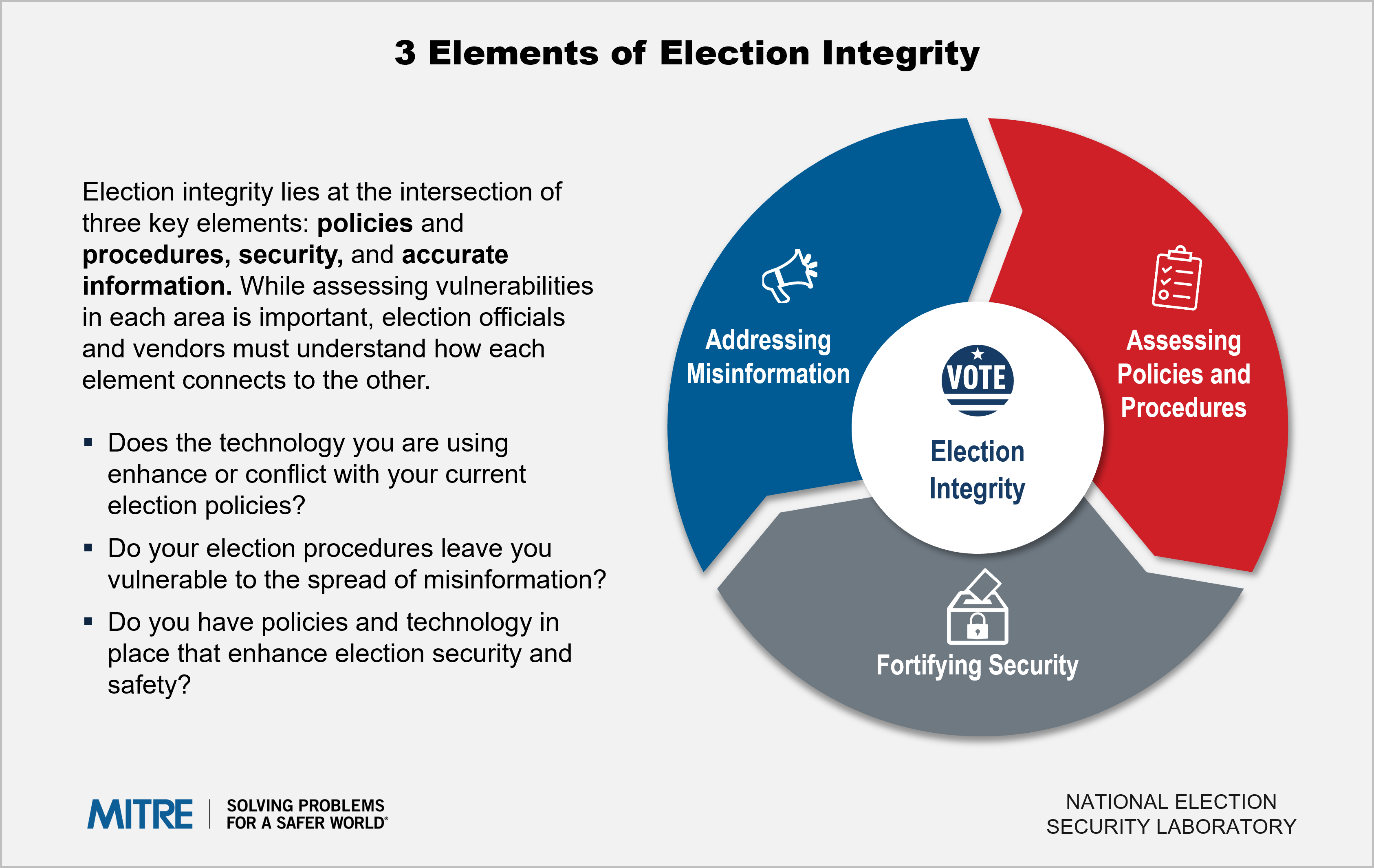
Assessing Policies and Procedures
Every state and local jurisdiction has its own voting system, with its own deadlines for voting and reporting, rules for data and equipment usage, and timing for how elections are carried out.
At the same time, voting machine manufacturers and election vendors have their own best practices and uses. Too often, the policies and procedures of a jurisdiction do not align with vendors’ best practices.
The result of this conflict? Less efficient voting systems and increased threats to election integrity.
Key policies and procedures questions
- Are there any potential conflicts within our election policy and procedure documents?
- Do our election policies and procedures enhance or hinder the efficiency of our elections?
- Do our technology and machinery purchases align with our policies and procedures?
- How do our election timelines and deadlines ensure a more trusted vote?
Fortifying Security
Election officials and vendors work each day to ensure safe and secure elections, but they face increasingly sophisticated threats.
As elections become more reliant on digital technology, cybersecurity attacks have become a realistic threat. From disrupting voter registration systems, hacking pollbooks or reports, or deploying ransomware on local or state voting systems, cyber adversaries have a growing set of tools at their disposal.
At the same time, ensuring the physical security, chain of custody, and access controls of physical voting equipment at the polling place is also vitally important.
Key security questions
- What election security threats is our election system vulnerable to?
- Has our election machinery been tested for key security vulnerabilities?
- What are likely physical security threats and how can we mitigate them?
- What cyber threats are our election technologies vulnerable to? How do we mitigate those threats?
Addressing Misinformation
One of the biggest threats to election integrity in today’s social media-fueled environment is the prevalence of misinformation and disinformation.
Misinformation comes in many forms: from the perpetuation of incorrect information about elections (i.e. when or how you can vote) to the questioning of election results.
Election officials must work to not only ensure that the right information is getting out, but also to disprove false information when it calls into question the integrity of an election.
Key misinformation questions
- How do we independently analyze election fraud claims?
- How do we identify and thwart inaccurate social media and online messages?
- How do we ensure trust in election procedures to prevent mistrust?